Privileged Access Management: Why It’s Critical for Your Business
Cybersecurity is no longer optional—it’s a business necessity. Yet, one of the most overlooked and easily exploited vulnerabilities in companies today is privileged access management (PAM). If your business isn’t actively managing who has access to what, you’re leaving the door wide open for cybercriminals, insider threats, and costly data breaches.
If you’re reassessing your company’s security posture this year, start with who has access to your most critical systems—and, more importantly, who shouldn’t. Let’s talk about why PAM matters, where businesses fail, and how to lock down your most sensitive data before it’s too late.
What Is Privileged Access Management (PAM) and Why Should You Care?
As we talked about in a previous blog, Privileged Access Management (PAM) is a security framework that controls, monitors, and restricts access to critical business systems. It ensures that only authorized personnel can interact with sensitive data, preventing unauthorized access, insider threats, and cyberattacks.
But here’s the problem: most businesses don’t know who actually has privileged access. IT admins, executives, and even third-party vendors may have credentials that could wreak havoc if they fall into the wrong hands. The stakes? Financial loss, reputational damage, regulatory fines, and a potential business shutdown.
Still think your business is safe? Let’s break down the most common access management failures and why they happen.
Where Businesses Fail: Common PAM Pitfalls
1. Over-Permissive Access: Too Many People Have the Keys
Most businesses operate with excessive trust, granting privileged access to too many employees. IT admins, HR staff, and executives often have credentials that go beyond their actual job needs. This is how insider threats and credential theft happen. One disgruntled employee or a stolen admin password can open the floodgates to data theft, sabotage, or unauthorized financial transactions.
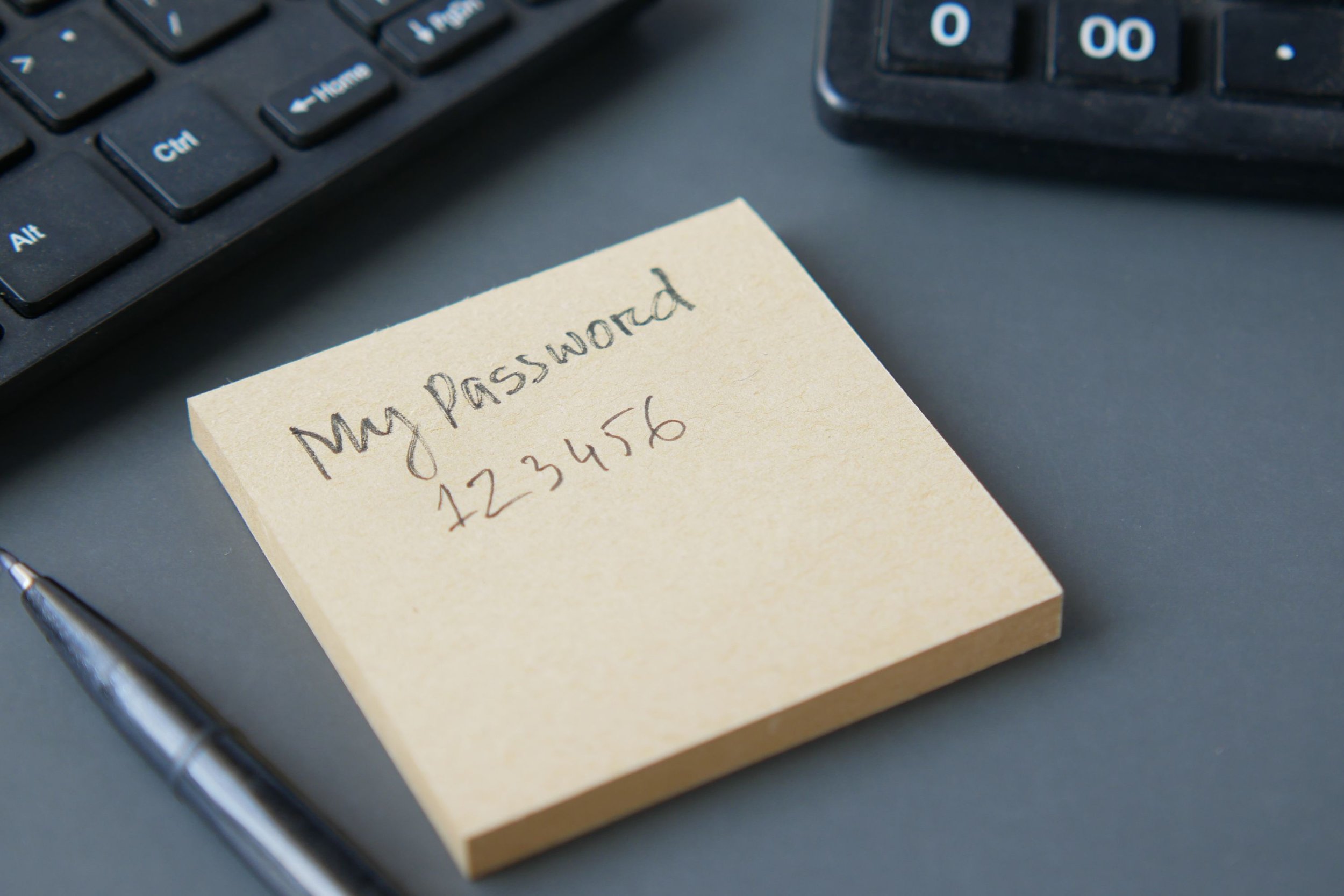
2. Weak Authentication: One Password Away from Disaster
If your privileged accounts are only protected by a username and password, you’re playing Russian roulette with your data. Passwords are easily phished, stolen, or cracked. Credential stuffing attacks, where hackers use previously breached credentials to access your systems, are happening every single day. If your IT admin reuses a password that was leaked in a previous data breach, congratulations—you’ve just handed hackers the keys to your kingdom. Use multifactor authentication methods where possible to help safeguard yourself against this.
3. No Session Monitoring: Blind Spots in Your Security
Most businesses have no idea who’s accessing privileged accounts, when, or why. If an unauthorized user logs into your system, how quickly would you know? Without session monitoring and logging, malicious activity can go undetected for weeks or even months. This is how cybercriminals operate—they infiltrate systems quietly, move laterally, and steal data without setting off alarms.
4. Dormant Accounts & Shadow IT: Unused Access Points for Hackers
Ever had an employee leave the company but their account stayed active for months (or years)? This is called a dormant account, and it’s prime real estate for cybercriminals. Hackers love abandoned accounts because they often go unnoticed. They can hijack an old login and quietly gain access to your systems without raising red flags. Similarly, Shadow IT (unauthorized applications employees use without IT approval) creates additional security risks.
How to Implement an Effective Privileged Access Management (PAM) Strategy
1. Conduct an Access Audit
Before making any changes, you need to know who has access to what. Audit all privileged accounts, including IT admins, executives, contractors, and third-party vendors. Identify unused, over-privileged, and unnecessary accounts.
2. Enforce Least Privilege Access (LPA)
Employees should only have access to what they absolutely need—nothing more. If an IT manager doesn’t need access to financial systems, revoke it. If a vendor doesn’t need admin access to your servers, don’t give it to them.
3. Require Multi-Factor Authentication (MFA)
MFA should be mandatory for all privileged accounts. No exceptions. This prevents stolen passwords from granting hackers instant access.
4. Implement Just-In-Time (JIT) Access
Instead of giving permanent privileged access, implement time-limited access. If an employee needs admin rights for a task, grant it for a specific time window, then revoke it automatically.
5. Monitor & Log Every Privileged Session
Use real-time monitoring, logging, and alerts to track all privileged activities. Detect suspicious behavior before it escalates into a breach.
6. Secure Remote Access for Third Parties
If vendors or contractors need access to your systems, use a secure gateway instead of granting full admin rights. Limit access by time, scope, and necessity.
Why PAM Should Be a Top Priority in 2025
Cyber threats are only getting worse. Ransomware gangs, insider threats, and nation-state hackers are constantly targeting privileged accounts to gain unauthorized access to company networks.
Here’s Why You Can’t Ignore PAM Any Longer:
80% of security breaches involve compromised credentials (Verizon Data Breach Report).
The average cost of a data breach is $4.45 million (IBM Cost of a Data Breach Report).
Ransomware attacks increased by 105% in 2023, with privileged accounts being a major target.
If you think your business is too small to be attacked, think again. Hackers don’t discriminate—they target weak links, and companies with poor privileged access management are easy prey.
How We Can Help
At LockStock, we specialize in securing privileged accounts and locking down sensitive data. Our PAM solutions help businesses:
✅ Identify and eliminate over-permissive access
✅ Implement multi-factor authentication and zero-trust security
✅ Monitor and log all privileged account activity in real-time
✅ Reduce attack surfaces with just-in-time access controls
We don’t just talk about cybersecurity—we deliver practical solutions that prevent breaches before they happen. If you’re serious about securing your privileged accounts in 2025, let’s talk.
Don’t Wait Until It’s Too Late
Privileged accounts are the #1 target for cybercriminals, yet most businesses still operate with lax access controls. If you don’t actively manage, monitor, and secure privileged access, you’re gambling with your company’s future. Don’t wait for a ransomware attack, insider threat, or regulatory fine to force your hand. Take control now.
Book a Consultation with us today. Your business depends on it.